Today, AES is used by governments, financial institutions, healthcare organizations, and technology companies worldwide. When you connect to your bank's website or encrypt a file with a modern tool, AES is almost certainly the algorithm at work.
How Encryption Works
Table of Contents
- 1. Symmetric Encryption
- 1.1 AES: The Gold Standard
- 2. Asymmetric Encryption
- 2.1 RSA: The Original Public-Key Algorithm
- 3. Symmetric vs Asymmetric: Comparison
- 3.1 When to Use Symmetric vs Asymmetric
- 4. Encryption in the Real World
- 4.1 HTTPS and TLS
- 4.2 End-to-End Encryption
- 4.3 Disk Encryption
- 4.4 Database Encryption
Encryption transforms readable data into scrambled, non-readable data called ciphertext. Decryption reverses this process and recovers the original data.
Think of encryption as a lockbox for your data. You place a message inside, lock it with a key, and send it across a network. Anyone who intercepts the box sees nothing but a sealed container. Only the intended recipient, who holds the correct key, can open it and read the contents.
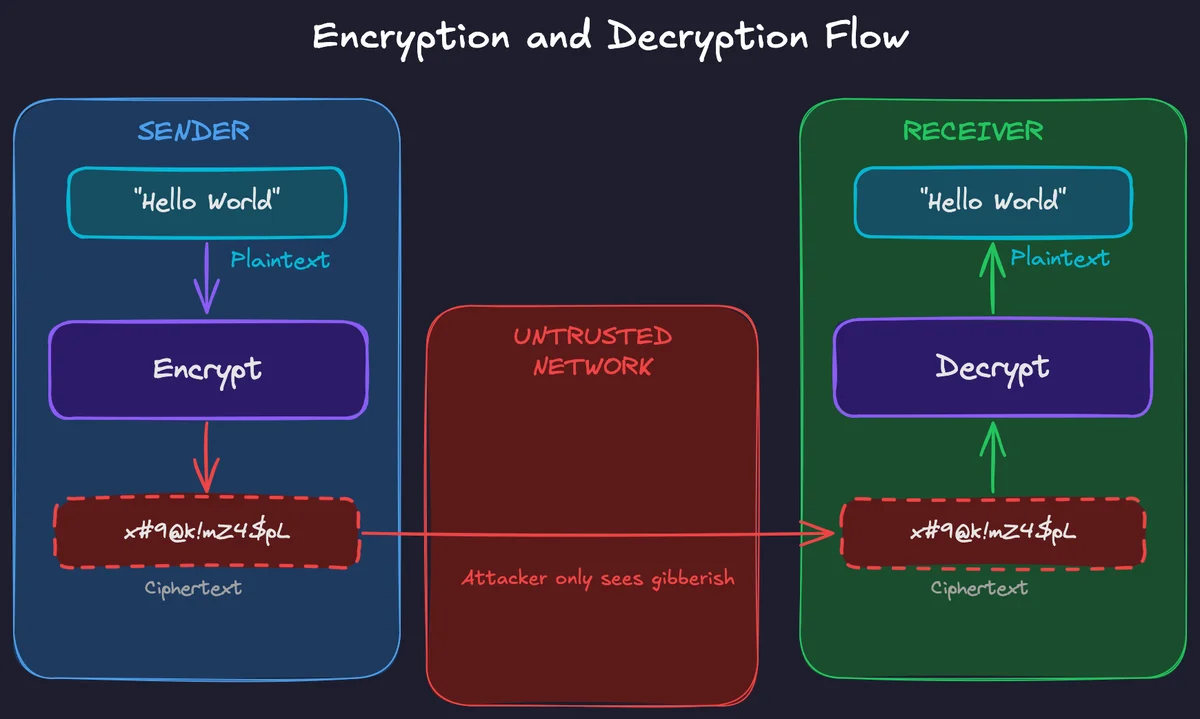
Every encryption system relies on two fundamental components:
- An Algorithm: a mathematical procedure for scrambling data
- A Key: the secret value that parameterizes the algorithm
The algorithm is public and well-studied. The security comes from the secrecy of the key, not the secrecy of the method. This principle is known as Kerckhoffs's principle, and it is a cornerstone of modern cryptography.
There are two types of encryption: symmetric encryption and asymmetric encryption.
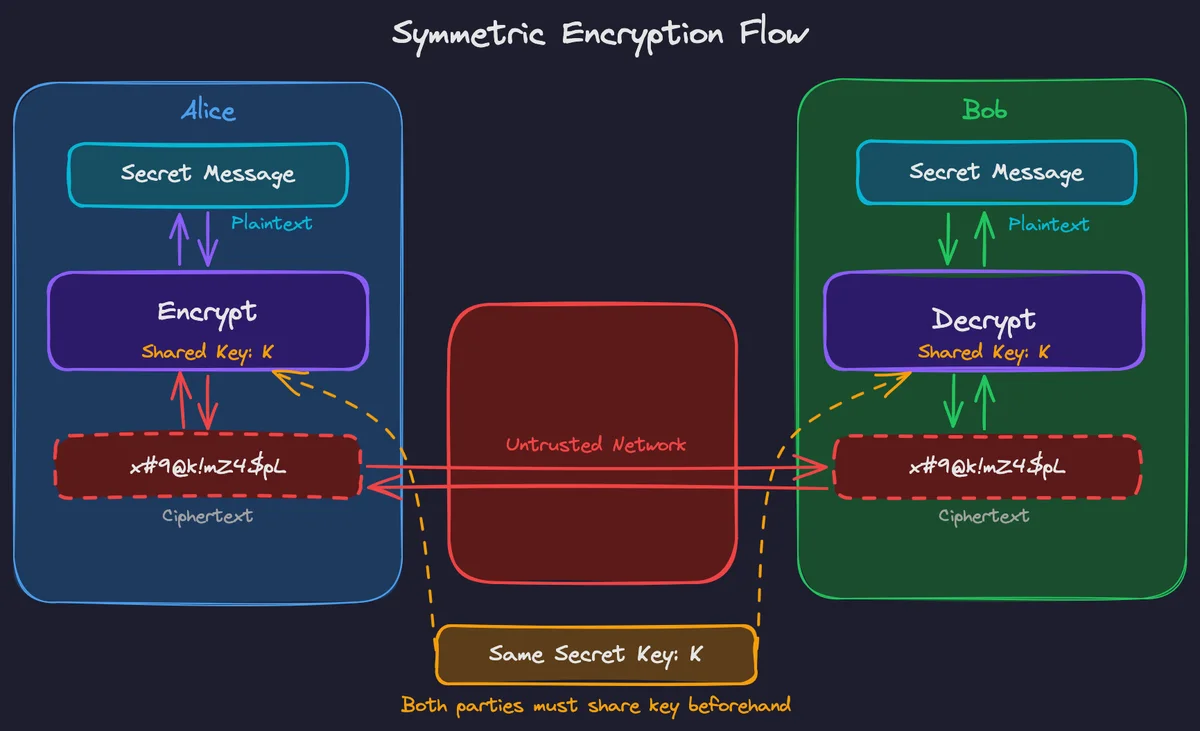
Symmetric Encryption
Symmetric encryption uses the same key for both encryption and decryption. The sender encrypts data with a secret key, and the receiver decrypts it with the identical key. It is the simplest and oldest form of encryption, and it remains the workhorse of modern data protection.
AES: The Gold Standard
AES is the most widely used symmetric encryption algorithm in the world. It won a public competition held by NIST, beating 14 other candidates to replace the aging Data Encryption Standard (DES), whose 56-bit key had become brute-forceable.
AES is a block cipher, meaning it encrypts data in fixed-size chunks of 128 bits. It supports three key sizes: 128, 192, and 256 bits. The key size determines the number of internal transformation rounds (10, 12, or 14 respectively) and the security strength, but the block size is always 128 bits. A 128-bit plaintext block goes in, and a 128-bit ciphertext block comes out.
To encrypt data larger than a single 128-bit block, AES uses a mode of operation that defines how blocks are chained together. ECB (Electronic Codebook) is the simplest mode, where each block is encrypted independently, but it is insecure because identical plaintext blocks produce identical ciphertext blocks, leaking patterns in the data. Modern systems use modes like GCM, CBC, or CTR, which ensure that even identical plaintext blocks produce different ciphertext.
Modern CPUs include dedicated hardware instructions called AES-NI that perform AES operations directly in silicon. This makes AES encryption essentially free in terms of performance, capable of encrypting billions of bytes per second on commodity hardware.
After over 25 years of public cryptanalysis, no one has broken full AES. The best known attacks are only marginally better than brute force and remain purely theoretical. For AES-256, a brute-force attack would require \(2^{256}\) operations, a number larger than the estimated atoms in the observable universe.
Another widely used algorithm is ChaCha20. For the sake of simplicity, we won't go through the ChaCha20 algorithm here, but you can read about it in more detail here: How does ChaCha20 work
Info
AES: Government-Grade Encryption
Asymmetric Encryption
Asymmetric encryption, also called public-key cryptography, uses a mathematically linked pair of keys: a public key and a private key. Data encrypted with the public key can only be decrypted with the corresponding private key. The public key can be shared freely with anyone, while the private key must be kept secret by its owner.
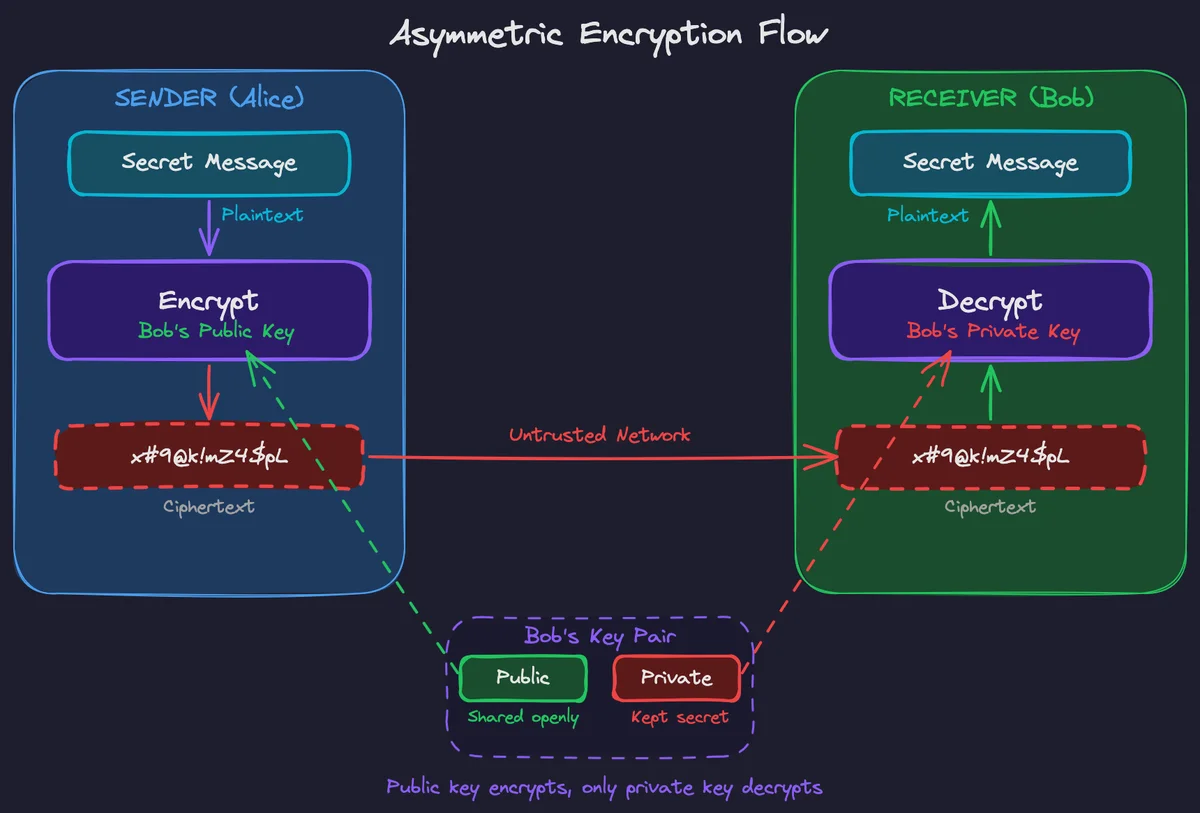
This design solves a fundamental challenge that symmetric encryption cannot: key distribution. With symmetric encryption, both parties must somehow securely agree on a shared secret key before they can communicate privately. Asymmetric encryption eliminates this problem. You can publish your public key to the world, and anyone can use it to send you encrypted messages that only you can read.
RSA: The Original Public-Key Algorithm
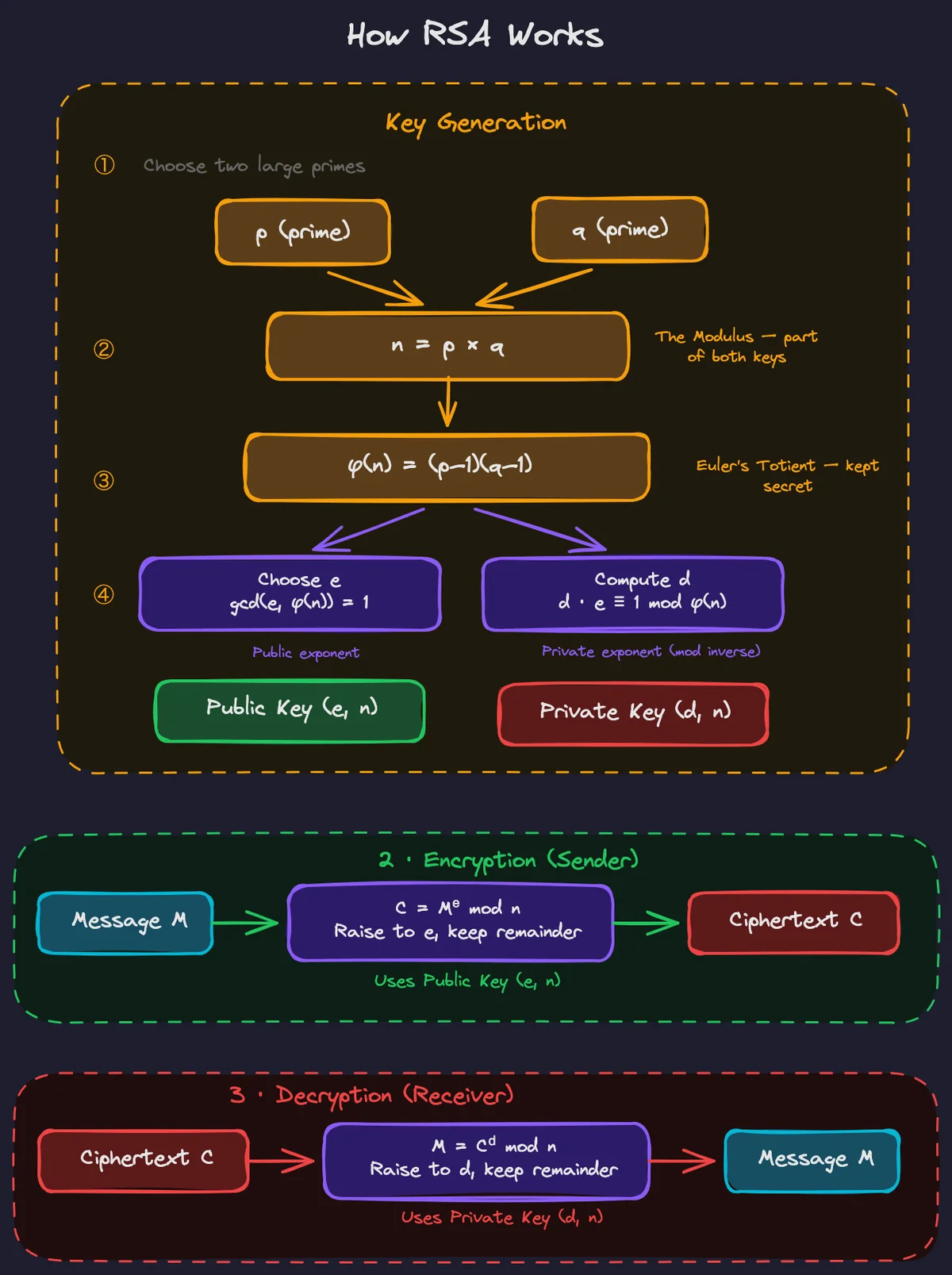
RSA (Rivest-Shamir-Adleman), published in 1977, was the first practical public-key cryptosystem. Its security is based on the mathematical difficulty of factoring the product of two very large prime numbers.
RSA key generation starts by selecting two large prime numbers, \(p\) and \(q\), and computing their product:
This value \(n\) becomes the modulus, which is the foundation of both the public and private keys. Next, we compute Euler's totient:
We then choose a public exponent \(e\) (commonly 65537) such that \(e\) and \(\phi(n)\) share no common factors. The public key is the pair \((e, n)\). The private exponent \(d\) is computed as the modular inverse of \(e\):
This means \(d\) is the unique value satisfying \(e \times d \equiv 1 \pmod{\phi(n)}\). The private key is the pair \((d, n)\).
To encrypt a message \(m\), the sender computes:
To decrypt, the recipient computes:
We can summarize this in the following equations:
The mathematics guarantees that raising to the power \(e\) and then to the power \(d\) (modulo \(n\)) returns the original message. Computing \(d\) requires knowing \(\phi(n)\), which requires knowing \(p\) and \(q\). Multiplying two primes is computationally trivial. However, reversing the process, meaning factoring their product back into the original primes, is computationally infeasible for sufficiently large numbers.
In practice, RSA is rarely used to encrypt data directly. The operation is slow and the message size is limited by the key length, so RSA is typically used to encrypt a small symmetric key (like an AES-256 key), which then encrypts the actual data. This is how protocols like TLS used RSA before the shift to elliptic curve key exchange.
Elliptic Curve Cryptography (ECC) is another modern approach to public-key cryptography. It achieves the same security as RSA but with dramatically smaller key sizes. You can read about it here: How Elliptic Curve Cryptography Works.
Symmetric vs Asymmetric: Comparison
Understanding the trade-offs between symmetric and asymmetric encryption is essential for choosing the right tool for a given security problem.
| Property | Symmetric Encryption | Asymmetric Encryption |
|---|---|---|
| Key count | One shared secret key | Key pair (public + private) |
| Speed | Very fast | 100-1000x slower |
| Key size for equivalent security | 128-256 bits | 2048-4096 bits (RSA) or 256-384 bits (ECC) |
| Key distribution | Requires pre-shared secret | Public key can be shared openly |
| Primary use cases | Bulk data encryption, disk encryption, database encryption | Key exchange, digital signatures, authentication |
| Common algorithms | AES, ChaCha20 | RSA, ECC (ECDSA, ECDH) |
When to Use Symmetric vs Asymmetric
Use symmetric encryption when both parties already share a secret key and you need to encrypt bulk data quickly. For example, encrypting files on disk or streaming encrypted video. Use asymmetric encryption when you need to establish a secure channel with someone you have never communicated with before, or when you need digital signatures for authentication and non-repudiation. In practice, most secure systems use both: asymmetric encryption to exchange a symmetric key, and then symmetric encryption for the actual data transfer.
Encryption in the Real World
Encryption is not an abstract concept confined to textbooks. It is embedded into nearly every digital interaction you have, working silently in the background to protect your data.
HTTPS and TLS
Every time you see the padlock icon in your browser's address bar, TLS is at work. Your browser and the web server perform a handshake that uses Diffie-Hellman key exchange (specifically ECDHE in TLS 1.3) to negotiate a shared session key without ever transmitting the key itself. Both sides contribute random values, and the mathematical properties of the exchange allow them to independently compute the same shared secret. All subsequent traffic is then encrypted with AES or ChaCha20 using that key. This prevents anyone on the same network from reading your traffic.
End-to-End Encryption
Messaging applications like Signal use end-to-end encryption (E2EE) so that only the sender and recipient can read messages. Not even the service provider has access to the decryption keys. Signal's protocol combines the Double Ratchet algorithm with X3DH key agreement.
Disk Encryption
Full-disk encryption tools like BitLocker (Windows), FileVault (macOS), and LUKS (Linux) encrypt the entire contents of a storage drive using AES. If a laptop is stolen or a hard drive is decommissioned, the data on the disk is unreadable without the decryption key. This is a critical safeguard for organizations that handle sensitive data, and it is required by compliance frameworks like HIPAA and PCI DSS for portable devices.
Database Encryption
Modern databases support encryption at rest (data stored on disk is encrypted) and encryption in transit (data sent between the application and the database is encrypted with TLS). Some databases also support column-level encryption, allowing organizations to encrypt only the most sensitive fields, such as Social Security numbers or credit card numbers, while leaving less sensitive data in plaintext for performance.
Log in to leave a comment.